www.vishnutechs.in is a Professional Educational and Entertainment Platform. Here we will provide you only interesting content, which you will like very much. We're dedicated to providing you the best of Educational and Entertainment, with a focus on dependability and Tech Tutorials. We're working to turn our passion for Educational and Entertainment into a booming online website. We hope you enjoy our Educational and Entertainment as much as we enjoy offering them to you.
10/06/22
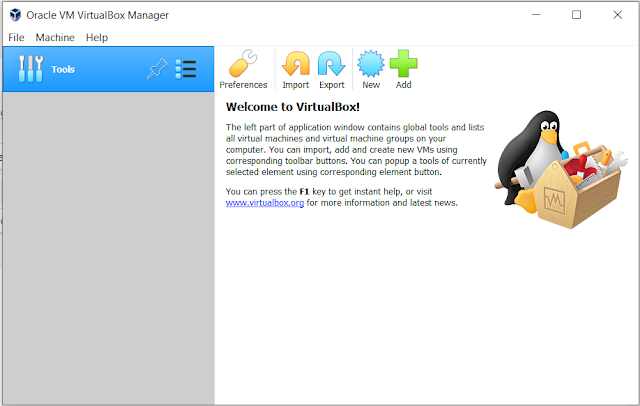
How to install VirtualBox on Windows 10/7/8 (32/64bit) | Deep Hacker | vishnutechs.in
What is Ethical Hacking ? | Types of Hackers | Deep Hacker | vishnutechs.in
What is Hacking? Types of Hacker
Hacking refers to the unauthorized or unauthorized access, manipulation, or exploitation of computer systems, networks, or digital devices. It involves activities aimed at gaining unauthorized access to data, bypassing security measures, and exploiting vulnerabilities for various purposes.
Note:
This site is for knowledge and educational purposes only, we do not promote or encourage any illegal activities.Your Responsible if you Get Used to That kind of Illegal Activities
For More Updates Join with Telegram Official Group
Hacking can be performed by individuals or groups with varying intentions, ranging from malicious activities to ethical hacking for security testing and research. Here are a few types of hacking:
1. Black Hat Hacking:
This refers to hacking done with malicious intent. Black hat hackers exploit vulnerabilities in systems to gain unauthorized access, steal sensitive information, disrupt services, or cause damage. They may engage in activities such as identity theft, data breaches, financial fraud, or spreading malware.
2. White Hat Hacking:
Also known as ethical hacking, white hat hackers perform hacking activities with the permission of the system owner. Their goal is to identify vulnerabilities and weaknesses in systems, networks, or applications to help improve security. They work to protect systems from potential black hat hackers by providing valuable insights and recommendations.
3. Gray Hat Hacking:
This type of hacking falls between black hat and white hat hacking. Gray hat hackers may access systems without explicit permission but have no malicious intent. They often expose vulnerabilities to the system owners and request a fee in return for disclosing the details of the vulnerabilities they discovered.
4. Hacktivism:
Hacktivists are hackers who carry out cyber-attacks or unauthorized activities to promote a specific social or political agenda. They may deface websites, leak sensitive information, or disrupt services to raise awareness or protest against certain issues.
5. Phishing:
Phishing is a technique used to deceive individuals into revealing sensitive information such as usernames, passwords, or financial details by disguising as a trustworthy entity. It often involves sending fraudulent emails or creating fake websites that mimic legitimate organizations or services.
It's important to note that hacking, unless authorized, is illegal and unethical. It can lead to serious consequences, including legal prosecution and damage to individuals, businesses, or organizations. Ethical hacking, however, is conducted within legal and ethical boundaries, with the goal of improving security and protecting systems from potential threats.
While hacking is generally associated with unauthorized activities and carries negative connotations, it's important to differentiate between illegal hacking and ethical hacking. Ethical hacking, also known as white hat hacking, involves hacking activities conducted with proper authorization and for legitimate purposes. Here are some benefits associated with ethical hacking and hackers:
1. Improved Security:
Ethical hackers help identify vulnerabilities and weaknesses in computer systems, networks, and applications. By simulating real-world attacks, they expose potential security flaws that can then be patched and strengthened, ultimately leading to enhanced overall security.
2. Vulnerability Assessment:
Ethical hackers perform comprehensive vulnerability assessments to identify potential weaknesses in systems. They can assess the effectiveness of security measures, including firewalls, intrusion detection systems, and access controls. This assessment helps organizations understand their security posture and take necessary steps to mitigate risks.
3. Early Threat Detection:
Ethical hackers can detect and report potential threats or security breaches before they can be exploited by malicious individuals. By proactively identifying vulnerabilities, organizations can take timely action to prevent data breaches, unauthorized access, or other cyber threats.
4. Protecting Sensitive Information:
Ethical hackers play a crucial role in protecting sensitive information, such as personal data, financial details, and intellectual property. By identifying weaknesses in security systems, they help organizations prevent unauthorized access and data breaches, safeguarding both individual and organizational assets.
5. Compliance and Risk Mitigation:
In many industries, compliance with specific regulations and standards is mandatory. Ethical hackers assist organizations in meeting these requirements by identifying vulnerabilities and recommending necessary security measures. They help mitigate risks associated with non-compliance and potential legal repercussions.
6. Security Awareness and Education:
Ethical hackers contribute to increasing security awareness among individuals, organizations, and the general public. Through their findings and recommendations, they help educate users about potential threats, safe online practices, and the importance of maintaining strong security measures.
It's crucial to remember that these benefits are associated with ethical hacking, which is conducted within legal and ethical boundaries. Unauthorized or malicious hacking carries severe legal consequences and can cause significant harm to individuals, organizations, and society as a whole.
Here are some benefits associated with ethical hacking:
Conclusion
Here are some frequently asked questions about Ethical Hacking:
1. What is ethical hacking?
Ethical hacking, also known as penetration testing or white-hat hacking, is the practice of testing computer systems, networks, and applications for vulnerabilities and weaknesses in a legal and authorized manner. The purpose is to identify and address security flaws to improve the overall security of the systems.
2. How is ethical hacking different from malicious hacking?
Ethical hacking is conducted with proper authorization and is intended to improve cybersecurity. It is performed by individuals who have legal permission to test systems for vulnerabilities. On the other hand, malicious hacking is unauthorized and aims to exploit security weaknesses for personal gain, causing harm or illegal activities.
3. Is ethical hacking legal?
Ethical hacking is legal when performed with proper authorization. Organizations often hire ethical hackers or engage third-party security firms to conduct penetration tests to assess the security of their systems. Unauthorized hacking, without explicit permission, is illegal and can lead to severe legal consequences.
4. What are the skills required to become an ethical hacker?
Ethical hacking requires a strong understanding of computer systems, networks, and programming languages. Key skills include knowledge of operating systems, networking protocols, web application development, and scripting languages. Additionally, problem-solving, critical thinking, and a continuous learning mindset are crucial for success in this field.
5. How can I learn ethical hacking?
There are various ways to learn ethical hacking. You can pursue formal education in cybersecurity or enroll in specialized courses and certifications such as Certified Ethical Hacker (CEH), Offensive Security Certified Professional (OSCP), or Certified Information Systems Security Professional (CISSP). Additionally, there are online resources, tutorials, and hands-on practice environments available for self-study.
6. What is the difference between a white-hat hacker and a black-hat hacker?
A white-hat hacker, also known as an ethical hacker, is someone who legally and ethically identifies vulnerabilities in computer systems to help improve security. They work with the system owners' permission and assist in fixing the identified issues. In contrast, a black-hat hacker is a malicious actor who hacks systems without authorization for personal gain, causing harm or engaging in illegal activities.
7. Can anyone become an ethical hacker?
Yes, anyone with a passion for cybersecurity and a willingness to learn can become an ethical hacker. While technical skills are essential, dedication, curiosity, and an ethical mindset are equally important. It's a field that requires continuous learning and staying updated with the latest technologies and security practices.
Remember, ethical hacking should always be conducted responsibly, within legal boundaries, and with proper authorization.
Ethical hacking promotes a safer and more secure digital environment by exposing vulnerabilities that could be exploited by malicious actors. It allows organizations to assess their security posture and address any weaknesses before they are compromised. By mimicking the tactics and techniques of real-world attackers, ethical hackers can identify potential entry.
10/05/22
How To Install Pip/PIP3 on Termux Android | Deep Hacker | vishnutechs.in
How to Install pip/pip3 on Termux
Hello Friends, Today we will learn about pip installation in Termux. PIP/PIP3 is a python program/module manager used to download python modules. If you are using Termux, you sometimes need to install some Python modules but don’t know how to use pip. Don’t worry today we will discuss everything about pip.
Before using PIP/PIP3, you need to install some required packages in your Termux.
First of all open termux and update and upgrade termux using given commands.
For More Updates Join with Telegram Official Group
What is PIP ?
PIP, which stands for "Pip Installs Packages," is a package management system used for installing and managing software packages written in the Python programming language. It is the standard package manager for Python.
PIP allows you to easily install, upgrade, and remove Python packages from the Python Package Index (PyPI), a repository of software libraries and modules maintained by the Python community. PyPI hosts thousands of packages that provide additional functionality to Python programmers, ranging from libraries for scientific computing to web frameworks and utility tools.
Here's a brief overview of how PIP works:
1. Installation:
PIP is typically installed alongside Python when you set up your Python environment. It is included with Python versions 3.4 and above by default.
2. Command-Line Interface:
PIP is primarily used through the command-line interface (CLI). You can open a terminal or command prompt and use various PIP commands to interact with the package manager.
3. Searching for Packages:
You can search for packages available on PyPI using the `pip search` command. For example, `pip search numpy` will show packages related to NumPy.
4. Installing Packages:
To install a package, you can use the `pip install` command followed by the package name. For example, `pip install numpy` will install the NumPy package on your system. PIP automatically resolves and installs any dependencies required by the package.
5. Upgrading Packages:
You can upgrade a package to the latest version using the `pip install --upgrade` command followed by the package name. For example, `pip install --upgrade numpy` will upgrade the NumPy package to its latest version.
6. Removing Packages:
To remove a package, you can use the `pip uninstall` command followed by the package name. For example, `pip uninstall numpy` will uninstall the NumPy package from your system.
7. Requirements Files:
PIP allows you to define project dependencies in a requirements file. This file lists all the packages required for your project, along with their specific versions. You can then install all the dependencies listed in the requirements file using the `pip install -r` command followed by the file name.
8. Virtual Environments:
PIP works well with Python's virtual environments, which allow you to create isolated environments for different projects. Virtual environments help manage dependencies separately for each project, avoiding conflicts. PIP can install packages into a specific virtual environment, ensuring that the project has its own set of dependencies.
PIP offers many other features and options, including package version control, package caching, and integration with build systems like setuptools. You can explore more about PIP and its commands by running `pip --help` or referring to the official PIP documentation.
Featured Post
Family Safety Guardian - Privacy & Privacy Policy
🛡️ Family Safety Guardian • Privacy & Data Protection Privacy Policy ...
-
8 Best Wifi Cracking Tools For Kali Linux,Ubuntu NOTE : This site is for knowledge and educational purposes only, we do not promote or enco...
-
How to Install BULLY on Kali Linux and Parrot. Hey Guys Today i'll show you How to install BullyTool On kali Linux and Parrot, for th...
-
Adsense Alternatives for 2023 Certainly, let's delve deeper into some of the best alternatives to Google AdSense with comprehensive de...